Identity Review | Global Tech Think Tank
Keep up with the digital identity landscape.
With a movement toward secure biometric authentication solutions, industries such as health care, immigration and national ID have adopted the technology as an easy way to prevent fraud and forgery. However, from irises to fingerprints to facial recognition, there are a variety of body parts that can be used. At Identity Review, we’ve analyzed the pros and cons of the most commonly used body parts and how they can create secure biometric identity solutions.
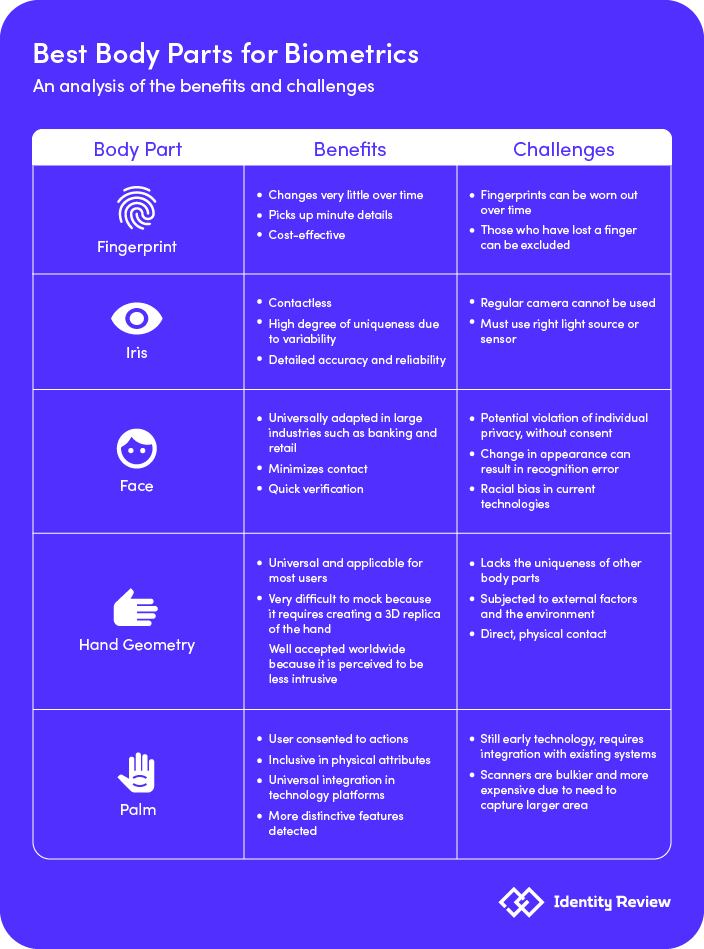
While most biometric systems leverage the iris or fingerprint, there are certain challenges. For instance, the iris is most accurate for biometrics, but the current model requires an iris scanner, which cannot be integrated with a regular camera. In addition, in order to do iris biometrics from a long distance, the technology must have an infrared spectrum, which also requires a camera with a very narrow field of view that has to follow the position of the face. This makes this body part and usage fragile, expensive and complicated.
Startups such as Redrock Biometrics have introduced other body parts for biometrics such as the palm. When co-founders Lenny Kontsevich and Hua Yang met as employees at Leap Motion, Apple released TouchID, sparking the hot conversation behind the biometrics field. Taking the entrepreneurial leap, the two left then left to start their own biometrics company: Redrock Biometrics, a provider of palm-print based biometrics for authentication and identification.
Redrock Biometrics’ technology allows for the combination of palm prints and/or subdermal veins, captured by a standard RGB camera and/or infrared camera, to produce a highly unique palm signature. Proprietary PalmID algorithms are capable of matching a newly captured palm signature with millions of previously registered signatures stored in a database in a fraction of a second.
Redrock Biometrics developed the app to deliver a passwordless sign-in experience for online users, combining security with multi-factor authentication. The PalmID Agent, registered with the user’s phone, poses as a username and the user’s palm becomes their password, which cannot be passed to someone or stolen. A certified anti-spoofing detector in PalmID does not permit any replica of a palm to be accepted for a sign-in. “Signing in with social accounts is highly popular and convenient but it is not very secure,” says Lenny Kontsevich, a Co-Founder of Redrock Biometrics. “Multi-factor authentication is much more secure but requires additional effort.”
“It is like hundreds of fingerprints just by area, so it contains a lot more information than a single fingerprint,” says Kontsevich. “But also, an advantage of the palm is that it has features at a different scale, so if you have a bad camera, you won’t be able to capture all these ridges and minutiae necessary for a fingerprint machine. Instead, you will get these larger features, larger lines and crevices, and they also are highly unique.”
In addition, palm biometrics, in comparison to face biometrics, shows intentionality versus presence. When users are around their devices, it is not a deliberate action to show and capture your face. However, when conducting transactions with palms, it means that the user agreed to do the transactions.
According to Kontsevich, in addition to privacy, palm biometrics is also inclusive.
“For people with dark skin, facial biometrics is less reliable. And that’s understandable, because with darker skin, you have less contrast, and you just don’t see as many details, and accuracy diminishes, which is a very sensitive social factor. For the palm, it is the opposite. People with dark skin usually have the crevices and lines on the palm—they’re kind of a little bit pigmented, so it actually increases the contrast of the features of the palm.”
Some other companies that provide palm biometric technologies include Fujitsu PalmSecure and Normee.

Fingerprint recognition and biometrics can replace passwords and ID cards and is one of the most widely available biometric solutions in the market. Fingerprint biometrics can pick up minute details such as orientation, ridges, arches, loops, whorls and pores, helping to use these points to confirm the user’s identity.
Fingerprints change very little over a lifetime, helping to ensure the longevity of the personal data, and are also cost-effective in helping to set up small hand-held scanners with a high level of accuracy.
However, fingerprint biometrics do have a degree of exclusivity to it. For older adults who have a lifetime history of manual work, their fingerprints might be worn out and cannot be detected by the system. In addition, those who have lost fingers or an entire hand would also be excluded from taking advantage of this technology.
Companies that provide fingerprint biometric technologies include Aware, Precise Biometrics, HID Global and Telpo.

Located between the cornea and the lens of the eye, the iris has characteristics that make it inherently unique and can be recognized from a distance. It has a false rejection rate of just 0.1-0.2% compared to other biometric solutions such as fingerprints, which have a 2%-3% false rejection rate.
Iris recognition typically involves two stages: enrollment, and then verification. In the enrollment stage, the pupil is scanned for the first time and is stored in the database for future authorizations. In the verification stage, the biometric system cross-checks the database to make sure that the data matches.
With its detailed accuracy and reliability, the iris is an appealing choice for verifying identity. It can help to ensure hygiene, as the iris can be scanned from a distance and does not require physical contact. The mathematical patterns of the iris also remain stable throughout one’s life but also have high degree of randomness that allows variability by 244 degrees-of-freedom and entropy by 3.2 bit per square millimeter.
However, if the subject is unconscious or dead, using iris biometrics won’t work, as the scanners must detect the movement of the iris. It also cannot be used by a regular camera, and must be used with an IR light source and sensor in order to ensure accuracy.
Companies that provide iris biometric technologies include CLEAR, TECH5 and IDEMIA.

The facial recognition technology is expected to grow to $9.6 billion by 2022, according to a report from Allied Market Research. Its systems are created using Closed-Circuit Television (CCTV) cameras that can analyze images, videos and live action. This allows the databases to determine identity paired with machine learning and artificial intelligence capabilities.
Facial biometrics can be used to enforce the law, enhance security and prevent crime. Many airports are already implementing facial recognition technologies at check-in, as the Department of Homeland Security predicts that it will be used on 97% of travelers by 2023. In addition, some hotels are allowing customers to skip check-in without a key using facial biometrics. And just like the iris, it minimizes contact and offers quick verification.
However, its biggest con is the public’s concern on violating individual privacy. For instance, San Francisco recently banned using facial biometrics in public spaces by police. The technology is also still a work in progress, meaning that any changes in appearance such as facial hair or face marks, can deceive the platform. This issue can also occur due to a change in camera angles.
Recently, a federal study confirmed that there is an embedded racial bias in facial recognition systems, which proved that Asian and African American people were 100 times more likely to be misidentified than white men depending on the algorithm and search function.
Companies that provide facial biometric technologies include iProov, Onfido and Aratek.

Hand geometry is based on the palm and fingers structure and can be used to identify users by the shape of their hands. Hand geometry is universal, as most individuals have one hand that can be scanned, even if there are any physical deformities. It’s also viewed as non-invasive in terms of privacy.
However, the hand geometry lacks the data and unique features of other body parts that are much more complex, like the iris. It is also subjected to the external environment and factors such as weight loss and injuries. Furthermore, it requires direct contact.
Companies that provide hand geometry biometric technologies include Ingersoll Rand and Inception Technologies.

ABOUT THE WRITER
Kevin Lu is a press and content strategist at Identity Review, where he writes about the intersection between media, tech ethics and social innovation. His work focuses on the data economy and its potential for creating social change in our world.
Contact Kevin Lu at kevin@identityreview.com.
Do you have information to share with Identity Review? Email us at press@identityreview.com.